Logic App is a new generation integration platform available in Azure. Being a serverless technology, there is no upfront hardware and licensing cost. That leads to a faster time to market. Because of all these features, Logic App is picking up pace in the Integration world.
Because Logic Apps are hosted in cloud, it’s not straight forward to access on-premise network hosted data sources from Logic Apps. To overcome that limitation, Microsoft introduced “on-premise data gateway”.
The gateway acts as a bridge that provides quick data transfer and encryption between data sources on-premises and your Logic Apps. All traffic originates as secure outbound traffic from the gateway agent to Logic Apps through Azure Service Bus Relay in background.
Currently, the gateway supports connections to the following data sources hosted on-premises:
|
|
Part 1: How does the Logic App on-premise data gateway works?
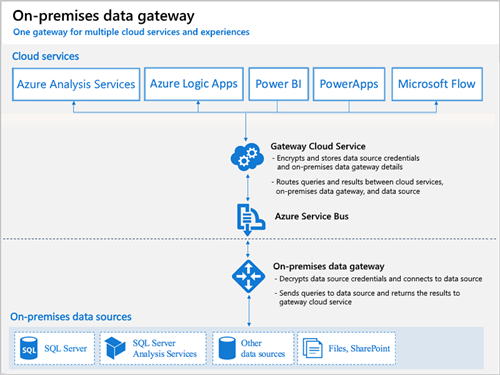
- The gateway cloud service creates a query, along with the encrypted credentials for the data source, and sends the query to the queue for the gateway to process.
- The gateway cloud service analyzes the query and pushes the request to the Azure Service Bus.
- The on-premises data gateway polls the Azure Service Bus for pending requests.
- The gateway gets the query, decrypts the credentials, and connects to the data source with those credentials.
- The gateway sends the query to the data source for execution.
- The results are sent from the data source, back to the gateway, and then to the gateway cloud service. The gateway cloud service then uses the results.
Part 2: How to install the on-premises data gateway?
Before we install on-premise data gateway, it’s very important to take following points into consideration:
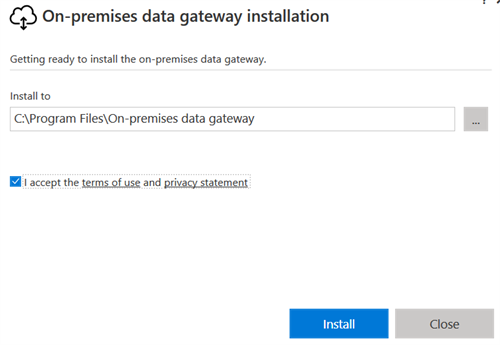
- Download and run the gateway installer on a local computer. Link: http://go.microsoft.com/fwlink/?LinkID=820931&clcid=0x409
- Review and accept the terms of use and privacy statement. Specify the path on your local computer where you want to install the gateway.
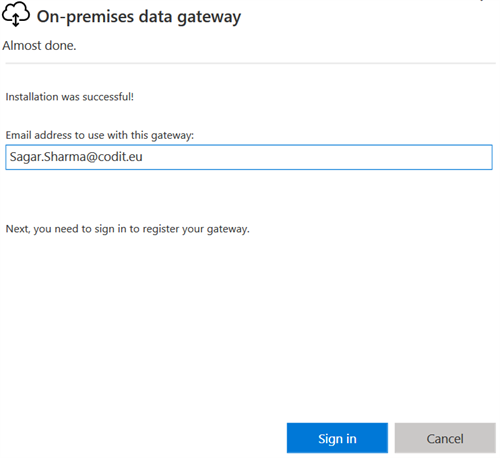
- When prompted, sign in with your Azure work or school account, not a Microsoft account.
- Now register your installed gateway with the gateway cloud service. Choose “Register a new gateway on this computer”. Provide a name for your gateway installation. Create a recovery key, then confirm your recovery key.
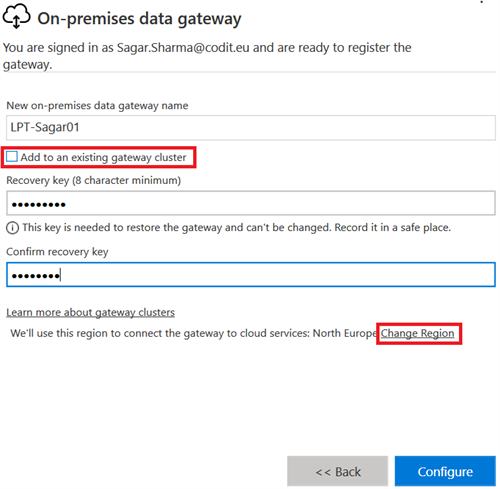
In order to achieve high availability, you can also configure the gateway in cluster mode. For that select “Add to an existing gateway cluster”. To change the default region for the gateway cloud service and Azure Service Bus used by your gateway installation, choose “Change Region”. For example, you might select the same region as your logic app, or select the region closest to your on-premises data source so you can reduce latency. Your gateway resource and logic app can have different locations. - Click on Configure and your gateway installation should be ready. Now we need to register this on-premise installation in Azure. For that log-on to your Azure subscription. Make sure you use the azure subscription which is associated with your work/school tenant. Create new resource of type “On-premises data gateway”
- Enter some name of your gateway. Choose subscription and resource group. Make sure you choose the same location as you selected during the gateway installation. You should be able to see the name of your gateway installation after choosing the same location
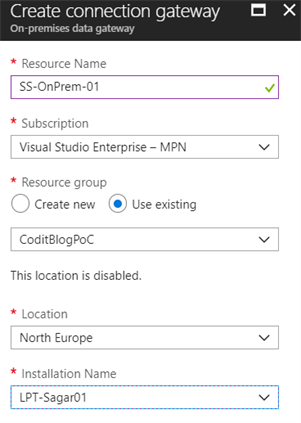
- Click on create and within a moment you will be able to use the on-premise gateway in your Logic App.
- You will be able to choose on-premise gateway installation to access on-premise hosted data sources in supported connectors.
For example:
-
- File System
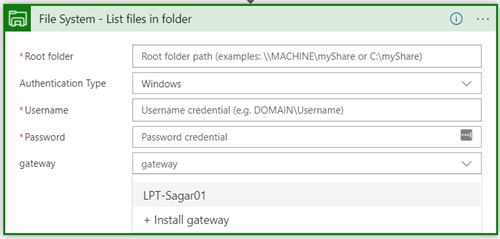
- File System
-
- SQL Server
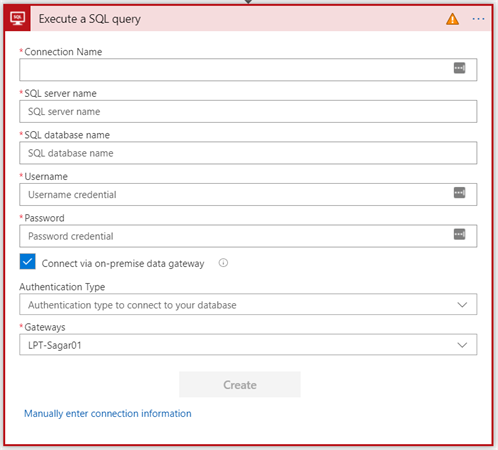
- SQL Server
Some important things to keep in mind
- The on-premise data gateway is firewall friendly. There are no inbound connections to the gateway from the Logic Apps. The gateway always uses outbound connections.
- Logic App on-premise data gateway also supports High availability via Cluster configuration. You can have more than one installation of gateway and configure them in cluster mode.
- When you install the gateway on one machine, it can connect to all hosts with in that network. So there is no need to install a gateway on each data source machine rather one in each network.
- Install the on-premises data gateway only on a local computer. You can’t install the gateway on a domain controller.
- Don’t install the gateway on a computer that turns off, goes to sleep, or doesn’t connect to the Internet because the gateway can’t run under those circumstances. Also, the gateway performance might suffer over a wireless network.
- During installation, you must sign in with a work or school account that’s managed by Azure Active Directory (Azure AD), not a Microsoft account.
You can find all official limitations around logic apps at https://docs.microsoft.com/en-us/azure/logic-apps/logic-apps-limits-and-config
Configure a firewall or proxy
- The gateway creates an outbound connection to Azure Service Bus Relay. To provide proxy information for your gateway, see Configure proxy settings.
- To check whether your firewall, or proxy, might block connections, confirm whether your machine can actually connect to the internet and the Azure Service Bus. From a PowerShell prompt, run this command-
Test-NetConnection -ComputerName watchdog.servicebus.windows.net -Port 9350
-
- This command only tests network connectivity and connectivity to the Azure Service Bus. So, the command doesn’t have anything to do with the gateway or the gateway cloud service that encrypts and stores your credentials and gateway details.
- Also, this command is only available on Windows Server 2012 R2 or later, and Windows 8.1 or later. On earlier OS versions, you can use Telnet to test connectivity. Learn more about Azure Service Bus and hybrid solutions.
- If TcpTestSucceeded is not set to True, you might be blocked by a firewall. If you want to be comprehensive, substitute the ComputerName and Port values with the values listed under Configure ports in this article.
- The firewall might also block connections that the Azure Service Bus makes to the Azure datacenters. If this scenario happens, approve (unblock) all the IP addresses for those datacenters in your region. For those IP addresses, get the Azure IP addresses list here.
Configure ports
- The gateway creates an outbound connection to Azure Service Bus and communicates on outbound ports: TCP 443 (default), 5671, 5672, 9350 through 9354. The gateway doesn’t require inbound ports.
| Domain names | Outbound ports | Description |
| *.analysis.windows.net | 443 | HTTPS |
| *.login.windows.net | 443 | HTTPS |
| *.servicebus.windows.net | 5671-5672 | Advanced Message Queuing Protocol (AMQP) |
| *.servicebus.windows.net | 443, 9350-9354 | Listeners on Service Bus Relay over TCP (requires 443 for Access Control token acquisition) |
| *.frontend.clouddatahub.net | 443 | HTTPS |
| *.core.windows.net | 443 | HTTPS |
| login.microsoftonline.com | 443 | HTTPS |
| *.msftncsi.com | 443 | Used to test internet connectivity when the gateway is unreachable by the Power BI service. |
- If you must approve IP addresses instead of the domains, you can download and use the Microsoft Azure Datacenter IP ranges list. In some cases, the Azure Service Bus connections are made with IP Address rather than fully qualified domain names.
Want to read more about on-premise data gateways?
Check out the sites below:
- https://docs.microsoft.com/en-us/azure/logic-apps/logic-apps-gateway-connection
- https://docs.microsoft.com/en-us/azure/logic-apps/logic-apps-gateway-install#gateway-cloud-service
Thanks for reading!
P.S.: In the last couple of months, I have extensively worked on Logic Apps and on-premise data gateway. So, feel free to contact me if you have any questions.
Subscribe to our RSS feed