Security testing
Property-Based Testing
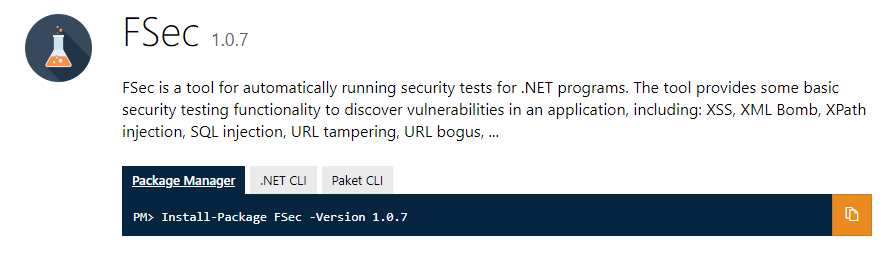
Introducing FSec
I wanted to find a way to combine both the security aspect and property-based testing. I knew that it would need to have input generators that can do things like generating different kinds of “injection” inputs so that we can verify if we’re vulnerable to security attacks.
So I started working on a package called FSec which provides input generators for security testing and can also be used in property tests.
The package is written in F# but has also a C# friendly API. I recommend that you brush up on Property-Based Testing and the FsCheck package because FSec uses the same approach to write generators. I chose this method because FsCheck is the most well-known package for writing properties in .NET.
Automating SQL injection vulnerability discovery with FSec
FSec.sqlInject generator that generates different types of injection strings, both valid and invalid, to make sure that the original query is altered in an unexpected way.- ,
- ;
- —
- 1′ or 1=1–
- 999999 or 1=1 or 1=1
Automating URL bogus vulnerability discovery with FSec
Http module comes from the FSharp.Data package.http://example.com with some required query parameters: category, style and size all with their own generator and builds a new URL with these required query parameters but also with a whole series of different query parameters.http://example.com?a0000001="c"&c0000003="<2"&category=""&d0000004=<null>&l0000012="n"&size="i"&style=<null>Other Exposed Functionality
FSec.dicAttack: John the Ripper dictionary generator Generates weak passwords used for a dictionary attack.FSec.fileIllegalNames: Illegal file name generator to validate the file uploading mechanism. Generate file names with semicolons, reserved names, percent sign, ampersand, …FSec.xmlBomb: XML Bomb input generator: An XML bomb is a message composed and sent with the intent of overloading an XML parser (typically HTTP server). It is block of XML that is both well-formed and valid according to the rules of an XML schema. It is a type of XML Denial of Service (DoS) attack. (more info: https://en.wikipedia.org/wiki/Billion_laughs)FSec.zipBomb: Creates a zip file bomb having a depth and width representing the different levels the zip bomb should have.- …
Conclusion
Subscribe to our RSS feed